Is Your SMB NAS Secure? Protect Your Business Data with SMB 3.0
In today’s increasingly digital landscape, the security of your SMB (Small and Medium-sized Business) NAS (Network Attached Storage) environment is of utmost importance. However, many organizations may be unaware that their current setup could be leaving their valuable data vulnerable to potential threats. Utilizing outdated protocols like CIFS/SMB 2.x exposes businesses to security risks, highlighting the critical need to transition to more secure alternatives such as SMB 3.x.
Why SMB 3.0 Matters:
The introduction of SMB 3.0 by Microsoft marked a significant leap forward in data security standards. With its end-to-end encryption support, SMB 3.0 ensures robust protection for data transmission, shielding it from potential eavesdroppers and unauthorized access. Whether you’re transferring sensitive documents or performing routine tasks like printing, SMB 3.0 guarantees that your data remains secure throughout its journey.
MoSMB’s Advanced Security Features:
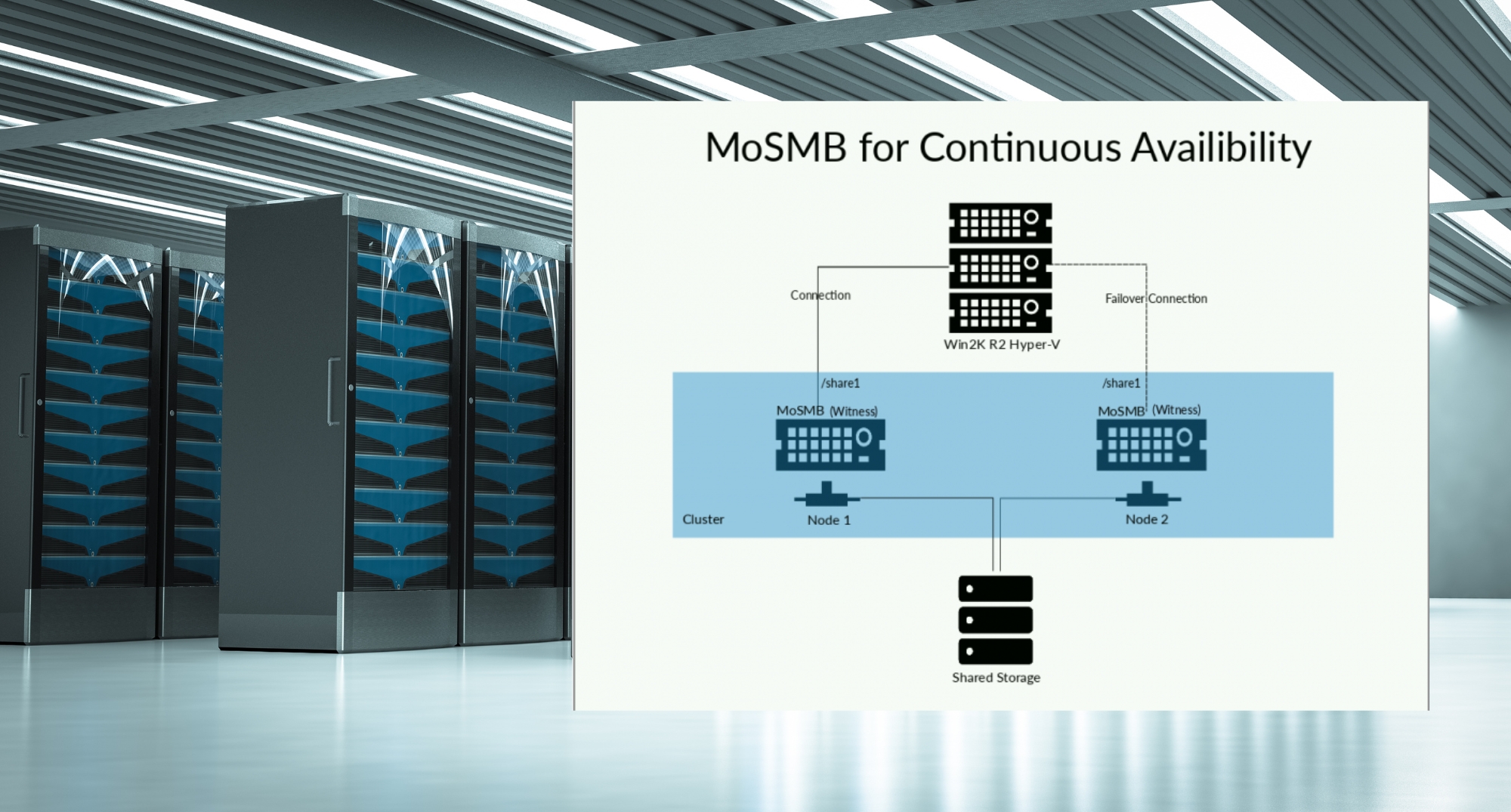
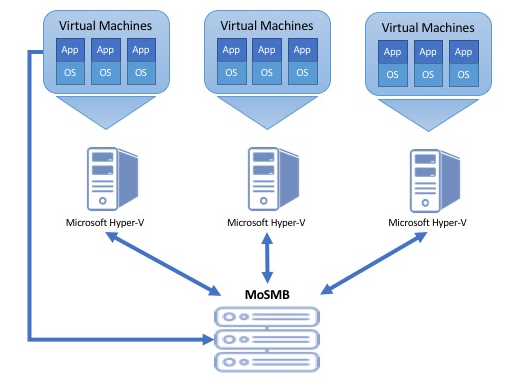
Leading the charge in SMB 3.0 adoption is MoSMB, a trusted provider of NAS solutions with a strong emphasis on security. MoSMB offers a comprehensive array of security features designed to safeguard your data against evolving threats:
- Full compliance with SMB 3.0 standards, ensuring adherence to the latest security protocols and industry best practices.
- Planned compliance with SMB 3.1.1 by May 2016, demonstrating a commitment to staying ahead of emerging security challenges and maintaining compatibility with future technologies.
- Robust user and domain authentication mechanisms to effectively manage access permissions and control data integrity.
- Advanced message signing and encryption capabilities to prevent unauthorized access and mitigate the risk of data tampering or interception.
- Support for widely recognized authentication protocols such as Kerberos and NTLMSSP/NTLMv2, bolstering security measures and ensuring compatibility with existing infrastructure.
- Flexible security configurations that allow for tailored settings on a per-share basis or across the entire file server, providing granular control over data access and protection.
- Integration of built-in security features eliminates the need for additional software, streamlining deployment and reducing maintenance overhead.
- Leveraging the AES-128-CCM algorithm for superior performance and efficiency, leveraging CPU AES acceleration to optimize data protection without compromising system resources.
- Future-proofing your security strategy with planned compliance with SMB 3.1.1, which includes the adoption of the AES-128-GCM algorithm for enhanced encryption and improved performance in high-demand environments.
Experience MoSMB’s Security Benefits:
Ready to elevate your SMB NAS security to new heights? Experience the peace of mind that comes with MoSMB’s advanced security features. Take advantage of the evaluation version available on Ryussi Cloud and explore the seamless integration and robust protection offered by MoSMB across a diverse range of use cases. With MoSMB, you can rest assured that your data is shielded from potential threats, allowing you to focus on driving your business forward with confidence.
Don’t compromise on data security. Upgrade to SMB 3.0 with MoSMB and safeguard your valuable assets from potential threats. Visit our website today to learn more about MoSMB’s security features and start your risk-free evaluation on Ryussi Cloud. Protect your data with MoSMB – your trusted partner for SMB NAS security in an ever-evolving digital landscape.